Several recent articles describe Chinese government plans for predictive policing software to help authorities identify potential terrorists and subversives, and prevent attacks and protests before they occur. The pre-crime data platform in construction will harness and analyze citizens’ behavioral data—such as online activity, financial transactions, travel patterns, and acquaintances—to predict which individuals are at risk of committing terrorism. This follows last year’s plans for a nationwide “social credit” database ranking citizens on their trustworthiness. Shai Oster at Bloomberg reports:
China’s effort to flush out threats to stability is expanding into an area that used to exist only in dystopian sci-fi: pre-crime. The Communist Party has directed one of the country’s largest state-run defense contractors, China Electronics Technology Group, to develop software to collate data on jobs, hobbies, consumption habits, and other behavior of ordinary citizens to predict terrorist acts before they occur. “It’s very crucial to examine the cause after an act of terror,” Wu Manqing, the chief engineer for the military contractor, told reporters at a conference in December. “But what is more important is to predict the upcoming activities.”
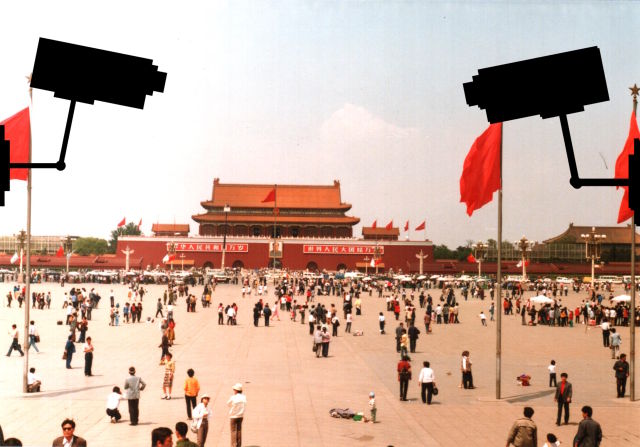
[…] Much of the project is shrouded in secrecy. The Ministry of State Security, which oversees counterintelligence and political security, doesn’t even have its own website, let alone answer phone calls. Only Wu, the engineer at China Electronics Technology, would speak on the record. He hinted at the scope of the data collection effort when he said the software would be able to draw portraits of suspects by cross-referencing information from bank accounts, jobs, hobbies, consumption patterns, and footage from surveillance cameras.
The program would flag unusual behavior, such as a resident of a poor village who suddenly has a lot of money in her bank account or someone with no overseas relatives who makes frequent calls to foreigners. According to Wu, these could be indicators that a person is a terrorist. “We don’t call it a big data platform,” he said, “but a united information environment.” In China, once a suspect is targeted, police can freeze bank accounts and compel companies to hand over records of his communications. [Source]
At Ars Technica, Sean Gallagher writes that the massive data collection effort going into the project is aided by new anti-terror legislation passed in December which could compel foreign tech companies to assist Chinese authorities in data acquisition. Also last year a draft cybersecurity law was unveiled which would allow authorities to tighten online information controls in the name of national security.
The Chinese government has plenty of data to feed into such systems. China invested heavily in building its surveillance capabilities in major cities over the past five years, with spending on “domestic security and stability” surpassing China’s defense budget—and turning the country into the biggest market for security technology. And in December, China’s government gained a new tool in surveillance: anti-terrorism laws giving the government even more surveillance powers and requiring any technology companies doing business in China to provide assistance in that surveillance.
The law states that companies “shall provide technical interfaces, decryption and other technical support and assistance to public security and state security agencies when they are following the law to avert and investigate terrorist activities”—in other words, the sort of “golden key” that FBI Director James Comey has lobbied for in the US. For obvious reasons, the Chinese government is particularly interested in the outcome of the current legal confrontation between the FBI and Apple over the iPhone used by Syed Farook. [Source]
Defense One’s Patrick Tucker looks at some of the latest developments in machine learning and artificial intelligence that have been made in China as part of its data collection drive:
[…C]ollecting massive amounts of data leads inevitably to the question of how to analyze it at scale. China is fast becoming a world leader in the use of machine learning and artificial intelligence for national security. Chinese scientists recently unveiled two papers at the Association for the Advancement of Artificial Intelligence and each points to the future of Chinese research into predictive policing.
One explains how to more easily recognize faces by compressing a Deep Neural Network, or DNN, down to a smaller size. “The expensive computation of DNNs make their deployment difficult on mobile and embedded devices,” it says. Read that to mean: here’s a mathematical formula for getting embedded cameras to recognize faces without calling up a distant database.
The second paper proposes software to predict the likelihood of a “public security event” in different Chinese provinces within the next month. Defense One was able to obtain a short demonstration of the system. Some of the “events” include the legitimately terrifying “campus attack” or “bus explosion” to the more mundane sounding, “strike event” or “gather event,” (the researchers say this was the “gather” incident in question.) all on a scale of severity from 1 to 5. To build it, the researchers relied on a dataset of more than 12,324 disruptive occurrences that took place across different provinces going back to 1998. [Source]
Data security and privacy issues also exist concerning popular Chinese web and mobile applications. In a recently released report, researchers at the University of Toronto’s Citizen Lab provide an in-depth analysis of how the Baidu Browser mobile application manages user data. The report identifies various security issues that puts users at risk of exposing their personal data, including web search terms and hardware identification. Below are key findings from the report:
Key Findings
- Baidu Browser, a web browser for the Windows and Android platforms, transmits personal user data to Baidu servers without encryption and with easily decryptable encryption, and is vulnerable to arbitrary code execution during software updates via man-in-the-middle attacks.
- The Android version of Baidu Browser transmits personally identifiable data, including a user’s GPS coordinates, search terms, and URLs visited, without encryption, and transmits the user’s IMEI and a list of nearby wireless networks with easily decryptable encryption.
- The Windows version of Baidu Browser also transmits a number of personally identifiable data points, including a user’s search terms, hard drive serial number model and network MAC address, URL and title of all webpages visited, and CPU model number, without encryption or with easily decryptable encryption.
- Neither the Windows nor Android versions of Baidu Browser protect software updates with code signatures, meaning an in-path malicious actor could cause the application to download and execute arbitrary code, representing a significant security risk.
- The Windows version of Baidu Browser contains a feature to proxy requests to certain websites, which permits access to some websites that are normally blocked in China.
- Analysis of the global versions of Baidu Browser indicates that the data leakage is the result of a shared Baidu software development kit (SDK),1 which affects hundreds of additional applications developed by both Baidu and third parties in the Google Play Store and thousands of applications in one popular Chinese app store. [Source]
Citizen Lab Director Ronald Deibert discusses the risks and “collateral damage” that can result from flaws in Baidu’s code:
What does that risk represent in real terms? Say you had Baidu Browser loaded on your mobile device and you connected to a wifi hotspot controlled by a criminal, spy, or some other nefarious group, maybe at a conference hotel, a coffee shop, or an airport. People with access to those networks would have been able to send malware to your phone disguised as a Baidu update and take over your phone and do anything they want with it. (Thankfully, it appears this issue has now been fixed by Baidu after our security disclosure).
[…] The report also illustrates a series of larger concerns related to the multiplication of applications, devices, and “things” that are connected to each other and the Internet, and which follow us around relentlessly. Insofar as applications such as these leak personally identifiable information, they become attractive targets for state intelligence agencies and other threat actors. We know this from the Snowden disclosures and comments made by senior intelligence officials. And you can bet if the FVEYs see it this way, other lower-tier countries and threat actors will do so eventually (if they are not already). Seemingly trivial bits of data leaked out that connect back to users become a very convenient “hook” or “selector” for intelligence analysts. With that IMEI number or serial number in hand, an analyst can go back in time and make connections with other individuals, places, points of data, or events that can be seriously incriminating.That may not matter to everyone who feels they have “nothing to hide” (although even in those cases people should still worry about crime, identity theft, etc.), but it can affect high risk users in life threatening ways.
All of this research underscores a pretty scary scenario we’re heading into, illustrated by one of the most remarkable aspects of the findings. […] [Source]