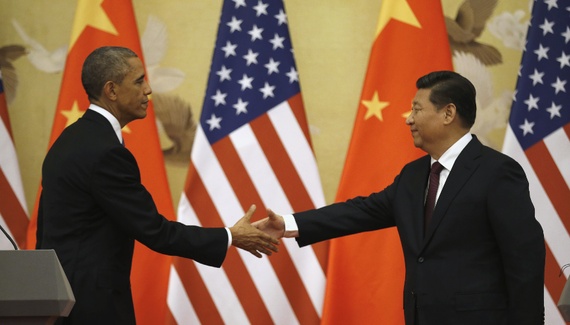
After years of mounting tensions over hacking, Chinese President Xi Jinping’s state visit to the U.S. last month brought an unexpected, if non-binding, accord. “Neither country’s government,” the two sides agreed, “will conduct or knowingly support cyber-enabled theft of intellectual property […] with the intent of providing competitive advantages to companies or commercial sectors.” They further pledged “to establish a high-level joint dialogue mechanism on fighting cybercrime and related issues.” “The question now,” President Obama commented, “is are words followed by actions.”
While both sides hailed the agreement, initial reactions from other quarters were mixed. James Lewis of the Center for Strategic and International Studies had been dismissive of Xi’s pledge to refrain from commercial theft earlier in the trip. But he described the subsequent deal as “a significant step forward,” and praised the Obama administration’s “clever” use of the threat of sanctions to gain leverage. At the Council on Foreign Relations, Robert Knake called it a “massive concession” from China, and “masterful diplomacy” by the U.S., adding that “the Obama Administration has been playing three dimensional chess and they won.” His colleague David Fidler described the announcement as “gobsmacking” and “a remarkable result of cyber statesmanship by Presidents Obama and Xi” which, beyond the bilateral relationship, “gives the United States an opportunity to push more credibly for countries to accept this norm and anchor it in international law.” Dmitri Alperovitch of security firm Crowdstrike similarly welcomed “a strategic inflection point,” “a watershed moment,” and “a tremendous victory for the Obama administration.”
The Wall Street Journal, on the other hand, labeled the agreement a “mirage,” and the official statements on it “an elaborate way of saying that the two sides agreed to nothing,” pointing out that Xi had continued to deny any involvement in the forbidden activities. When asked if he believed that Chinese attacks would stop as a result, U.S. Director of National Intelligence James Clapper told the Senate Armed Services Committee, bluntly, “no.” The U.S. should “trust but verify,” he added, but “such malicious cyber activity will continue and probably accelerate until we establish and demonstrate the capability to deter malicious state-sponsored cyber activity.”
On Friday, The Washington Post’s Ellen Nakashima and Adam Goldman reported a possible sign of almost unprecedented action on China’s part, with the detentions of several accused hackers ahead of the deal:
“We need to know that you’re serious,” was the way one individual familiar with the matter described the message. “So we gave them a list, and we said, ‘Look, here’s these guys. Round them up.’”
Now, administration officials are watching to see if China will follow through with prosecutions. A public trial is important not only because that would be consistent with established principles of criminal justice, but because it could discourage other would-be hackers and show that the arrests were not an empty gesture.
[…] Catherine Lotrionte, who teaches international law and cyberpolicy at Georgetown University and is a former CIA lawyer, said she had been skeptical that the pact was more than words. But China’s arrests, she said, “makes the U.S. government look much smarter coming into this agreement” with Xi. “You want to see the Chinese do something,” she said. “This would be one of those things that I want to see. It is a good-faith move by the Chinese.”
She too, however, cautioned that there must be follow-through. “You want to watch over the next couple of months for action, for the cessation of attacks,” she said.
[…] One complication, said a second individual familiar with the case, is that Chinese prosecution would entail the United States sharing evidence linking the cyberintrusions to the individuals. And to do so could compromise sensitive information on how the U.S. government tracked the suspects. [Source]
Chinese Foreign Ministry spokesperson Hua Chunying commented on Tuesday:
Q: It is reported that the Chinese side arrested in accordance with information offered by the US some hackers suspected of cyber espionage. Please confirm and give us more details. If it is true, is that an example of cyber security cooperation between China and the US, or is that just a quick fix to hold back US sanctions against China?
A: I have noted the relevant report. The Chinese government holds a clear-cut and consistent position on opposing cyber attacks and espionage and combating all forms of hacking activities in accordance with the law. Whoever commits cyber attacks and espionage at whatever time and whatever place in China violates China’s national law and will face legal sanctions once caught.
Both China and the US are major internet users who enjoy broad shared interests and face common challenges in the field of cyber security. During President Xi Jinping’s visit to the US, the two sides had thorough discussions and reached important consensus on the issue of cyber security. We hope that the two sides would work in concert to implement the consensus and make the issue of cyber security a new point of cooperation between China and the US instead of a source of friction. [Source]
While Hua evaded the matter of threatened sanctions, others suggested that they were likely decisive. From Yale Law School’s Graham Webster in his U.S.-China Week newsletter, for example:
The revelation that the Chinese government detained alleged hackers identified by the U.S. government before Xi’s visit likely suggests how far the Chinese side was willing to go in efforts to save the visit and at least temporarily avoid U.S. sanctions. Of course, secret detention does not send a message publicly within China, and the answer to Obama’s question—”Are words followed by actions?”—hinges on whether public prosecutions follow on this or other cases and whether the subsequent parallel statement has any force. To me, news that such detentions preceded Xi’s visit further calls into question whether China’s government intends to follow through in enforcement and norm creation, rather than merely doing what was necessary to save the visit. If not for the joint language that emerged during the visit, you might think of the arrests as similar to pre-summit symbolic releases of political prisoners when human rights was higher on the U.S. agenda with China. [Source]
At Lawfare Blog, though, Harvard Law School’s Jack Goldsmith argued that the threat of sanctions alone would not have been enough:
[… I]f China blinked, something more must have been threatened. Perhaps that something more was hinted at by President Obama ten days ago at a Business Roundtable speech:
“[I]ndustrial espionage and stealing trade secrets, stealing proprietary information from companies [is] an act of aggression that has to stop. And we are preparing a number of measures that will indicate to the Chinese that this is not just a matter of us being mildly upset, but is something that will put significant strains on the bilateral relationship if not resolved. … [I]f we wanted to go on offense, a whole bunch of countries would have some significant problems. And we don’t want to see the Internet weaponized in that way.”
This seems like a threat to use offensive cyber attacks in response to IP theft, which is a much more significant threat than mere selective economic sanctions. Such offensive actions would of course mark a dangerous escalation that would invite in-kind retaliation that could cause the United States much suffering. There’s no way to know what the United States concretely threatened, or what risks it was willing to absorb. But if China really is pledging to accept the U.S. norm and change its behavior, the United States must have threatened much, much more than the selective economic sanctions that has dominated the headlines in the last few weeks. [Source]
Read more on Obama’s speech and other recent statements via CDT.
At the American Enterprise Institute, Claude Barfield had previously argued that sanctions should still go ahead, even after the agreement:
While one can hope that the summit did indeed mark a turning point on Chinese cyber theft, there are two reason for going forward with the legal action: first, it would underscore the seriousness with which the US holds these incursions. Cliché or not, actions do speak louder than words. And second, without leveling any cheap shots against the diplomacy of the Obama administration, it is a fair point to note that the world has seen the US blow past a number of “red lines.” In this case, after promising action, follow-through could help to redress that record. [Source]
Answering questions on the visit from a congressional subcommittee, Richard Bejtlich of security firm FireEye suggested that sanctions would not appear soon:
The last consequence that we appear to have available is sanctions. The President mentioned that in the event the Chinese don’t appear to be upholding their end of this agreement, that the administration would pursue activities, possibly through U.S. trade rep, or through the WTO, through some mechanism … the executive order that they signed earlier this year gives them authority to impose sanctions as well. My personal opinion is we’re not going to see sanctions anywhere within say a six month period, and honestly that starts to get towards the end of the Obama administration, and he may simply say “I’m going to hold off, just for the rest of my time.” [Source]
On the subsequent news of the alleged hackers’ detentions in China, Bejtlich commented at Brookings:
Overall, this development is significant because it is a concrete action by the Chinese government that moves beyond the words shared by Presidents Xi and Obama in late September. However, it does present some risks that perceptive American officials should consider before pressing for further action.
[…] It is easy for China-watchers to be cynical about developments in the digital arena, but this is a promising development. What matters now is how far the United States presses its position. It is important to welcome the news but be wary of reciprocal, asymmetric Chinese demands. [Source]
There has been widespread but unconfirmed speculation that the recent detainees, like the five suspected hackers indicted by the U.S. last year, are connected with China’s military. Security expert The Grugq commented on this possibility:
China arrest hackers wanted by the US: it is a very strange world where army officers are arrested by their superiors for following orders.
— thaddeus e. grugq (@thegrugq) October 10, 2015
@yaelwrites yeah, we’ll need to see what actually happened. But the US advocating arresting officers is very weird. Bad precedent
— thaddeus e. grugq (@thegrugq) October 10, 2015
In any case, the PLA, which is widely suspected of involvement in the kind of hacking at issue, presents something of a wildcard. FireEye’s Bejtlich addressed the military issue in his congressional testimony:
First, consider President Xi’s posture prior to the September 25th press conference. In written answers to questions posed by the Wall Street Journal, President Xi claimed “The Chinese government does not engage in theft of commercial secrets in any form, nor does it encourage or support Chinese companies to engage in such practices in any way.” Combining this statement with his later declarations, it is possible President Xi is professing that the Chinese government does not hack, because he does not consider the People’s Liberation Army, Ministry of State Security, or other organizations conducting hacking operations to be part of his definition of “Chinese government.” Therefore, PLA units such as 61398, revealed by Mandiant in 2013, will continue to raid American companies, because Xi does not count them as government forces. [Source]
In the subsequent Q&A session, he added:
As far as the issue with the PLA, it’s entirely possible that the Chinese government could rather than direct the PLA or the MSS to conduct these operations, they could sort of take a Thomas Becket approach, say “wouldn’t it be great if someone could get us this information.” Or “there is a need, the government has a need for this sort of information,” and the military might pursue it on their own, or you may see a movement of people from those units into the Chinese private sector, where suddenly they become security companies or contractors who carry out this activity. We’ve called that the decentralized scenario at FireEye. Honestly, until the Chinese government changes its strategic decision to pursue Western technology and to abandon any sort of vulnerability or dependence on Western technology, they are going to continue to get this by any means necessary. [Source]
Similarly, from Adam Segal at the Council on Foreign Relations:
The other big issue is will the agreement increase, or reinforce, Beijing’s reliance on proxies to conduct cyber espionage. As a recent investigation in the Wall Street Journal shows, there is overlap between PLA and freelance hacking groups. During their press conference, President Obama said that President Xi told him, “with 1.3 billion people, he can’t guarantee the behavior of every single person on Chinese soil.” But what portion of hacking is government controlled is already murky and now there are reasons to muddy the waters even further. [Source]
The Jamestown Foundation’s Peter Mattis also commented at War On The Rocks:
[… T]he absence of the PLA in the agreement casts a shadow over the effectiveness of any mechanism to file requests about alleged violations of Chinese civilian and military intelligence collectors hacking foreign companies. The Ministry of Public Security and Ministry of State Security do not have the authority to enter PLA compounds to conduct investigations and make arrests. Other Chinese security organizations, like the State Secrets Bureau, have separate military elements and so also cannot access the PLA. The Ministry of National Defense is the PLA’s mechanism for dealing with non-military organizations; yet, even they are not a part of the Sino–American committee to handle law enforcement issues dealing with cyberspace.
[…] If Xi Jinping and the Chinese government intend to stand by the cyber affirmation, then a dramatic drop-off in Chinese cyber espionage should be visible within weeks because the PLA would be the first of the Chinese agencies involved to draw down systematically and redirect its resources — unless foreign observers have profoundly misread the party–PLA relationship. If such a drop-off is not seen, then the most likely explanation is that Xi had no intention of abiding by the affirmation. [Source]
Mattis also warned that differences in the two sides’ basic positions could set the agreement up to become “another broken promise”:
As others have noted, China views its activities in cyberspace in the commercial, economic, and national security realm as a part of comprehensive national power and protecting China’s developmental path. Accepting the U.S. interpretation requires Beijing to disaggregate its policy toolkit in unprecedented ways. Additionally, the vast scientific and industrial information complex in China serves to promote national development, not Chinese companies’ competitive advantage. […]
[…] Moreover, the fine distinctions that Americans want to draw between supporting commercial companies and collecting intelligence on foreign scientific developments and their related economic base also ask Beijing to accept U.S. government support to defense-industrial companies that now increasingly compete internationally, including with some Chinese firms. This seems like a little too much trust to ask of two governments that increasingly mistrust the intentions of one another — or at least of a Chinese government fearful that the United States secretly intends to subvert and change the regime.
[…] Probably more than any other issue, cyber has poisoned the well of U.S.–China relations as reports and leaks confirmed each side’s worst suspicions of the other’s activity in cyberspace. [Source]
Whatever the success or otherwise of the agreement, its “fine distinctions” limit it to a very specific category of attacks, as The Washington Post’s Henry Farrell explained:
The agreement does not address many of the more dramatic recent examples of Chinese spying, such as the apparent hack of the U.S. security clearance system, which led Washington to withdraw embassy personnel from Beijing for fear that the cover of CIA operatives has been blown. One excellent reason why the agreement doesn’t address this kind of spying is that the United States does it too, is very good at it, and doesn’t want to stop. US officials have expressed chagrin at the hacking of U.S. security clearances. They have also expressed some envy, and made it clear that if they could do the same to the Chinese government, they would.
Furthermore, the Chinese government can still hack U.S. companies, and steal their secrets with impunity. The only difference is that they cannot pass the secrets that they have learned to Chinese companies to give them competitive advantage. Gary Hufbauer at the Peterson Institute suggests that the “exact lines of demarcation” will mean that defense contractors remain fair game, while other companies, such as telecoms, might perhaps be off limits. This seems to misunderstand the agreement. The United States has not only been willing to hack into telecommunications companies, but also into energy companies, and, for that matter, universities and human rights organizations. It is unlikely that China’s sensibilities are any daintier. The agreement limits the goals of spying, not the targets being spied upon. [Source]
The hacking of military contractors recently warned of by the FBI and reported by The Daily Beast; attacks on Hillary Clinton’s email server reported by the Associated Press; and even the theft of data from mobile payment startup LoopPay for (the company claims) non-commercial purposes, reported by The New York Times, are all therefore exempt.
FireEye’s Bejtlich also highlighted the broad sweep of exceptions:
A final consideration for this agreement requires considering who is left out. The focus on US and Chinese companies ignores many other targets. These include so-called civil society organizations (CSOs), as well-documented in the recent report by the University of Toronto’s Citizen Lab titled Communities @ Risk. These CSOs include dissident groups inside and outside China, universities, think tanks, media organizations, lawyers, and human rights watchers. Companies in Europe, Asia, Africa, and elsewhere are not covered by the US-China agreement. Furthermore, the agreement mentioned the UN Group of Governmental Experts in the Field of Information and Telecommunications in the Context of International security, also known as the UN GGE, but it did not agree to implement its findings concerning critical infrastructure. Therefore, those systems continue to be held at risk, as will the government, military, intelligence, and law enforcement organizations of each country. [Source]
On Sunday, an extensive report in The Wall Street Journal placed the Sino-U.S. maneuvers in the context of “a frantic and destabilizing digital arms race” involving both state and non-state parties. The former were catalogued in a separate feature. For more on this wider context, see Eric Geller’s recent account of “The global struggle to prevent cyberwar” at The Daily Dot.